WEST LAFAYETTE – As hackers continue to attack U.S. electric grids, supply chains, manufacturing facilities, and other important infrastructure, the computers controlling these networks still don’t have the ability to distinguish between real and fake information, says a Purdue University cybersecurity expert.
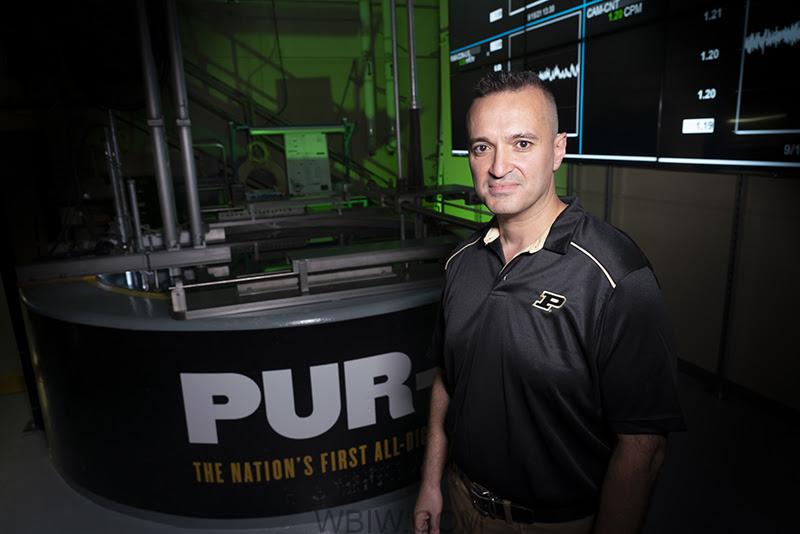
Hany Abdel-Khalik, an associate professor of nuclear engineering and researcher with Purdue’s Center for Education and Research in Information Assurance Security (CERIAS), can discuss:
- What digital monitoring platforms for critical infrastructure are lacking in terms of security.
- How artificial intelligence can be used to fool existing security techniques.
- What must be done to keep systems operational even when breached.
“By design, computers are slaves. They do what you tell them to do. They can’t tell the difference between real and false information, and that’s why they have to rely on a trustworthy source of information to tell them what to do,” Abdel-Khalik says. “If a computer had the self-awareness or covert cognizance, basically we’re saying that the computer can develop its own inner thoughts about how it interacts with the system that it’s used to control. And if it can do that, then it will be incorruptible. It will be able to tell the difference between real and fake.”
A video of Abdel-Khalik’s comments on critical infrastructure cyberattacks is available on Google Drive.
From studying the efficiency of nuclear reactor systems and how they respond to equipment failures and disruptions, Abdel-Khalik has become familiar with advanced computational techniques used by critical infrastructure systems.
Earlier this year, Abdel-Khalik and his students published papers demonstrating how an algorithm they developed could enable computer models of critical infrastructure systems to have the “self-awareness” and “self-healing” needed for more decisively foiling hacks. Even if an attacker is armed with a perfect duplicate of a system’s model, any attempt to introduce falsified data would be immediately detected and rejected by the system itself, requiring no human response, the team’s studies have shown.
Abdel-Khalik’s research group is working with startups to advance this new strategy to market.
“Critical infrastructures rely on computers to process data and do monitoring and control,” Abdel-Khalik says. “The rules that define the transmission and communication of trustworthy information are referred to as protocols. These protocols are standardized and used in various industries. Standardized protocols are good for operation.
“But at the same time, they are basically defining the job of the attacker – that is, to find the vulnerability in those protocols and pose as a trusted party. Once you pose as a trusted party, you can do one of two things. Either you deny service completely – which is a common form of attack that we have right now – or you can start providing false information to those systems. And that’s when things get really more dangerous.”
Information: Kayla Wiles, wiles5@purdue.edu
Source: Hany Abdel-Khalik, abdelkhalik@purdue.edu